In the evolving landscape of enterprise security, the integrity of your surveillance system depends not only on camera quality but on the network infrastructure that connects these critical endpoints. While organizations invest heavily in advanced surveillance hardware, many overlook a fundamental weakness: incomplete wireless network coverage that creates operational blind spots, packet loss, and system failures.
Wireless Access Points (APs) serve as the backbone of modern distributed security networks, enabling seamless communication between surveillance devices, network video recorders, and central management systems. However, strategic deployment requires far more than simply placing APs throughout a facility. The challenge lies in understanding RF propagation, mitigating interference, and designing redundant pathways that ensure continuous uptime for mission-critical security operations.
This technical guide examines the engineering principles behind effective wireless access point deployment for security infrastructure, providing enterprise IT teams and security architects with actionable frameworks to eliminate coverage gaps and optimize network performance across complex environments.

Understanding the Problem: Coverage Gaps in Security Networks
The Real Cost of Network Dead Zones
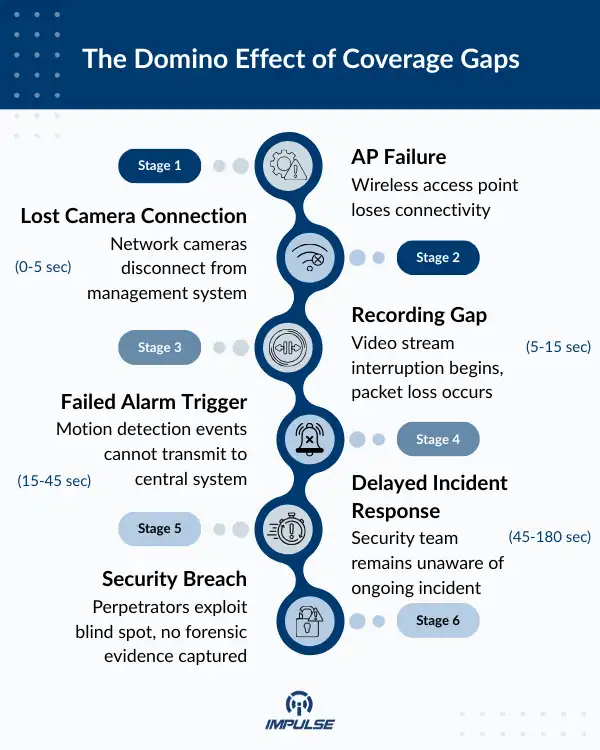
Coverage gaps in wireless infrastructure create cascading failures throughout security ecosystems. When surveillance devices lose connectivity—even momentarily—the consequences extend beyond simple data loss:
- Blind spot creation: Areas without adequate network coverage cannot support surveillance devices, leaving physical locations unmonitored
- Data packet loss: Intermittent connectivity causes fragmented video streams and corrupted recordings
- System latency: Weak signal strength introduces delays in real-time monitoring and alarm triggering
- Authentication failures: Edge devices repeatedly attempt network authentication, consuming bandwidth and processing resources
- Maintenance overhead: Technicians waste hours troubleshooting connectivity issues rather than addressing actual security concerns
Traditional approaches to wireless deployment treating APs as simple “signal broadcasters” fail to account for the demanding requirements of security video transmission, which requires sustained bandwidth, minimal jitter, and guaranteed quality of service (QoS).
Environmental Factors That Complicate Deployment
Modern facilities present unique challenges for wireless network design:
- RF interference from industrial equipment, IoT devices, and neighboring networks
- Physical obstructions including concrete walls, metal structures, and glass partitions
- Multipath propagation causing signal reflection and phase cancellation
- Dynamic environments where people, vehicles, and movable equipment constantly alter propagation characteristics
- Regulatory constraints limiting transmit power and channel selection
These variables make predictive modeling essential, yet many organizations deploy APs reactively adding equipment only after coverage problems emerge.
Agitating the Consequences: What Poor Planning Really Costs
Operational Impact
When wireless infrastructure fails to meet security system requirements, organizations face immediate operational challenges. Video management systems cannot maintain persistent connections to cameras, resulting in dropped frames during critical incidents. Network-attached storage systems receive incomplete data streams, creating gaps in forensic evidence. Real-time alerting mechanisms fail to trigger because event packets never reach the central monitoring station.
Consider a warehouse environment with network-connected dome cameras monitoring perimeter access points. If wireless infrastructure supporting the network backbone is inadequately positioned, cameras at the facility’s extremities may experience signal degradation during peak utilization precisely when surveillance coverage is most critical. Organizations must understand the relationship between enterprise-grade wireless network design and surveillance system performance to avoid these connectivity failures.
Financial and Compliance Implications
The financial burden of poor wireless infrastructure extends beyond immediate troubleshooting costs:
- Compliance failures: Regulatory standards often mandate continuous recording capabilities; gaps in coverage can result in substantial penalties
- Insurance implications: Claims may be denied if surveillance footage contains gaps during incident timeframes
- Reactive remediation: Emergency infrastructure upgrades cost 3-5x more than proactive planning
- Bandwidth waste: Inefficient topology creates unnecessary re-transmission overhead, requiring higher-capacity (and more expensive) backbone connections
- Shortened equipment lifespan: Devices constantly struggling with connectivity experience accelerated hardware failure rates
Organizations deploying cameras with computational capabilities discover that these processing features generate substantial metadata traffic requiring stable network connectivity for efficient transmission to central management systems. Understanding how PoE switches streamline network security deployments becomes critical for ensuring both power delivery and data transmission reliability. Without proper wireless infrastructure, the investment in intelligent cameras yields diminished returns.

Solution Framework: Strategic Wireless Access Point Deployment Methodology
Phase 1: Comprehensive Site Survey and RF Analysis
Effective wireless infrastructure begins with thorough environmental assessment:
Pre-Deployment Assessment
- Conduct professional RF site surveys using spectrum analyzers to identify interference sources
- Map physical obstructions and document construction materials affecting signal propagation
- Calculate coverage requirements based on device density and bandwidth demands
- Identify power availability for AP installation locations
Predictive Modeling
- Utilize heat mapping software to simulate coverage patterns before hardware installation
- Model multiple scenarios with varying AP placement to optimize signal strength and redundancy
- Calculate expected throughput considering real-world attenuation factors
- Design for 20-30% capacity overhead to accommodate future expansion
Phase 2: Architecture Design for Security Applications
Network Topology Considerations
Security networks demand specific architectural approaches:
- Controller-based management: Centralized wireless controller systems enable unified policy enforcement, seamless roaming, and rapid troubleshooting across distributed APs
- VLAN segmentation: Isolate surveillance traffic from general network activity using dedicated virtual LANs with appropriate QoS tagging
- Redundant pathways: Design mesh topologies where APs can relay traffic if primary backhaul connections fail
- Power over Ethernet (PoE) planning: Ensure adequate PoE+ (802.3at) or PoE++ (802.3bt) capacity for high-performance APs
Phase 3: Deployment and Integration
Installation Best Practices
Physical AP placement significantly impacts performance:
- Mount APs at optimal heights (typically 8-12 feet in office environments, adjusted for warehouse or outdoor settings)
- Orient antennas appropriately for coverage patterns (omnidirectional vs. directional)
- Maintain minimum separation distances from interference sources (microwave ovens, industrial motors, metal ducting)
- Document exact coordinates and configuration for each AP to facilitate troubleshooting
Integration with Surveillance Infrastructure
Network infrastructure must accommodate burst bandwidth demands that occur during PTZ operations. For instance, when deploying advanced PTZ camera systems with extended zoom capabilities and long-range IR illumination, zoom adjustments and pan-tilt movements generate significant data spikes that wireless backhaul systems must handle without degrading overall network performance. Proper PoE switch selection ensures adequate power delivery for these high-performance devices while maintaining network stability.
Edge computing applications utilizing cameras with onboard analytics generate processed video and metadata streams that require consistent network connectivity. The wireless infrastructure becomes an integrated component of the processing pipeline, not merely a transport mechanism. Organizations should consider optimizing IP camera installations alongside wireless infrastructure planning to ensure end-to-end system reliability.
Phase 4: Testing, Validation, and Optimization
Post-Deployment Verification
Comprehensive testing ensures coverage objectives are met:
- Perform actual throughput testing from surveillance device locations using representative traffic patterns
- Validate roaming behavior by moving test devices between coverage zones
- Stress-test network under maximum anticipated load conditions
- Verify QoS policies are correctly prioritizing surveillance traffic over other network activity
Continuous Monitoring and Adjustment
Wireless environments remain dynamic; ongoing management is essential:
- Implement network monitoring tools that track AP performance metrics, client connections, and interference sources
- Establish baseline performance metrics for proactive issue detection
- Conduct periodic re-surveys as facility layouts change or new interference sources emerge
- Maintain documentation of all configuration changes and performance observations
Advanced Considerations for Enterprise Deployments
Scalability and Future-Proofing
Organizations must design wireless infrastructure with growth in mind:
- Deploy enterprise-grade APs capable of firmware updates to support evolving standards (Wi-Fi 6E, Wi-Fi 7)
- Implement centralized management platforms that scale to hundreds or thousands of APs
- Design backbone network capacity with 3-5 year growth projections
- Plan for increased device density as IoT security sensors proliferate
Security Protocol Implementation
Wireless security networks face unique cybersecurity challenges:
- Implement WPA3-Enterprise with certificate-based authentication for device access
- Deploy network access control (NAC) systems to authenticate and authorize surveillance devices
- Establish separate management VLANs for AP administration
- Enable wireless intrusion detection systems (WIDS) to identify rogue access points
Outdoor and Harsh Environment Deployments
Extending wireless coverage to exterior areas and industrial settings requires specialized approaches:
- Select APs with appropriate IP ratings (IP65/IP67 for outdoor or industrial environments)
- Account for significantly increased attenuation in outdoor scenarios (no RF containment)
- Design for weather-related interference patterns that vary seasonally
- Implement redundant power systems (PoE + local battery backup) for mission-critical outdoor locations
Conclusion
Coverage gaps in wireless infrastructure represent more than technical inconveniences—they constitute fundamental vulnerabilities in security posture. Organizations that approach wireless access point deployment strategically, applying rigorous engineering principles and comprehensive planning methodologies, create surveillance ecosystems that deliver consistent performance, support advanced capabilities, and scale efficiently with operational requirements.
The investment in proper wireless infrastructure planning yields returns far exceeding the initial effort: reduced troubleshooting overhead, improved system reliability, enhanced security effectiveness, and infrastructure that adapts to technological evolution. By treating wireless networks as critical components of the security architecture rather than commodity infrastructure, organizations eliminate blind spots, optimize resource utilization, and ensure their surveillance investments deliver intended value.
As security technologies continue advancing with AI-powered analytics, 4K and 8K video streams, and edge computing capabilities, the underlying network infrastructure becomes increasingly critical. Organizations that master strategic wireless AP deployment position themselves to leverage these innovations effectively while maintaining the reliability and performance their security operations demand.
Impulse specializes in integrated security solutions that combine advanced surveillance hardware with robust network infrastructure, ensuring your security ecosystem operates at peak efficiency.


